We use cookies to enhance your experience and analyze site usage. You can at any time.
Showing 2 of 2 scenarios
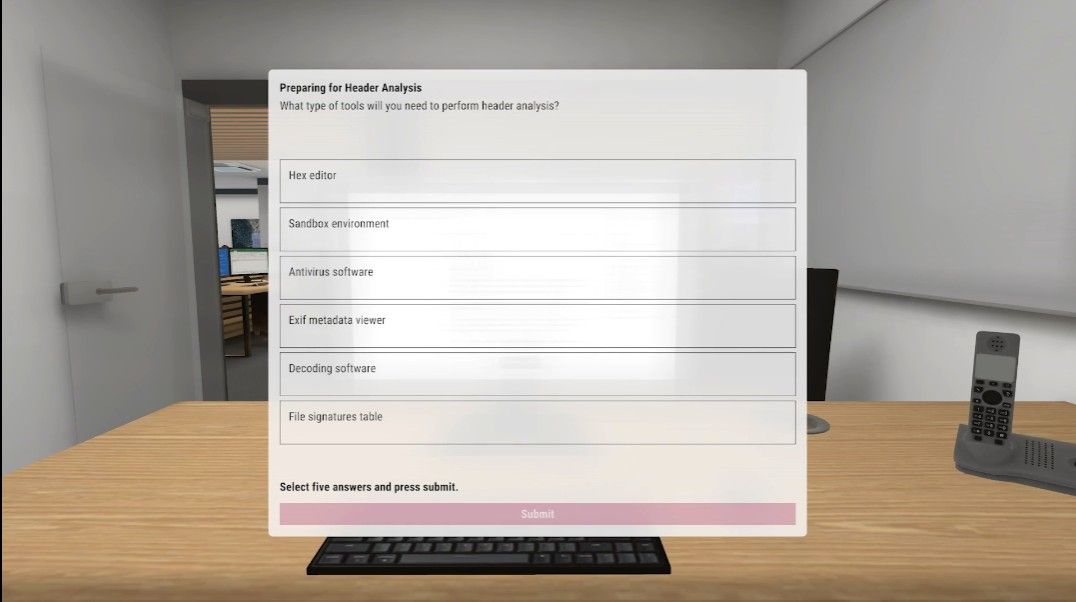
Work through a realistic phishing scenario where you analyse a suspicious email, identify threat indicators and decide on the safest course of action to protect organisational systems.

Work through a simulated DDoS attack where you analyse traffic patterns, apply mitigation techniques and maintain business continuity while preparing for post‑attack recovery.